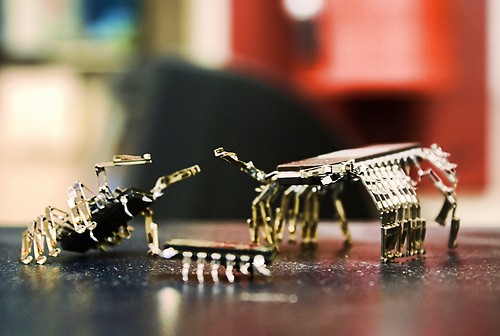
Through this blog post, I’m going to discuss the types of computer viruses and their painful effects on PC. I hope it would help you to protect your computer from hazardous programs.
Nowadays, the use of computer and internet has been rapidly increased. Together with it, the computer threats like spyware, Trojans, and worms are rising and get into the action severely.
So it is good to know the various types of computer viruses to protect your system from the malicious programs. Let me start with the definition of the computer virus with a fundamental question, what are computer viruses!
Let me start with the definition of the computer virus with a fundamental question, what are computer viruses!
What is Computer Virus?
A biological virus makes you sick!
Like the same, computer virus infects your programs and files on your PC. Yes, it is an executable program which affects the normal operation of the computer by damaging the contents of the hard disk.
It could cause frequent computer crashes, delete files, weakens computer memory and even reformat the hard drive.
How Do Computer Viruses Reach You?
Different types of computer viruses would reach you through the typical web activities like,
1. Opening email attachments from fake accounts.
2. Clicking inappropriate internet advertisements without understanding fully.
3. Installing/downloading the free games, toolbars or system utilities.
4. Visiting an infected web page
5. Setting up of software without licensing agreements.
6. Getting malware from websites through online ads because of their weak passwords or software flaws.
7. Inserting or connecting infected external device and disk.
8. Installing pirated software.
Not only with web activities, if you are not running the latest updates of your operating system and not using the good antivirus software, but computer viruses would also reach you quickly.
Read: A Simple Guide about Anti-virus program
Different Types of Computer Viruses
Many types of viruses in computer exist, and some famous names of computer viruses are as follows!
1. Macro Virus
A macro virus is a type of email virus which mainly targets to infect the programs that contain Macros like Microsoft Office files or all the similar types of files such as doc, pps, xls, MDB, etc.
It automatically infects all your macro files and also causes a sequence of typical actions performed automatically when the program starts. These types of virus tend to surprise victims by its behavior, but it is a harmful virus.
Mostly these types of virus are hidden in a documents or files which are shared through an email or networks.
Macro viruses which are most vulnerable:
Relax: Relax also called as W97M/Relax.C is an advanced macro virus threat that exhibits new ransomware worm like behavior. It’s the most dangerous model in the macro virus.
Bablas: W97M/ Bablas.aj is a macro virus which is also called a bablas. It’s a macro virus which has the oldest form of attacks but it is dangerous, but as the technology is increased it has been turned a moderate level macro virus.
Y2K: 097M/Y2K is a macro virus which is globally known as Y2K. Y2K spreads the infection from the initial document to all the documents. It prevents the users from working with macros files as it disables the options in macros.
2. Memory Resident Virus
Memory resident virus automatically fixes themselves in the computer memory, and if the operating system starts to run, it gets activated.
It is hidden out in the memory of the computer and allocates space to execute its code. It can easily corrupt the files that are recently used.
These type of virus affects the included files and programs.These viruses even force them to close or open unnoticeable and also sometimes they rename and copy as well.
Memory resident viruses that are highly vulnerable:
CMJ: Cmj is a memory resident virus where attackers often use to destroy systems.It is also known as the Trojan“BackDoor-CMJ”, and it’s having lots of models with this type of virus.
It was discovered in 2005. This virus mainly comes installed from the unknown program of hacked web pages, internet relay chat, peer-to-peer networks, etc.
Meve: Meve is a memory resident virus which is often called as e-mail worm. It was discovered in 2003, and it’s a high-profile virus in those days, its code name is “W32/COlevo@MM” the meve virus.
3. Overwrite Virus
Overwrite virus a kind of virus which deletes the information contained in the files or programs that it infects. Once these types of virus affect a file, then that file will become utterly useless as it will delete the complete original information in it.
Unfortunately, we can’t even restore the info as we must remove it completely therefore by losing original content. These type of virus replaces the file content, but it will not change the file size.
Overwrite virus which is highly vulnerable:
Trj.reboot: trj.reboot is an overwrite virus, which deletes the information easy then other overwrite virus.It’s a most destructive model in overwrite virus.
Trivial: trivial is an unwanted Trojan virus infection which is formerly called as “Trivial.88.D.” It is a overwrite virus which can destruct and make any software as useless.
4. Direct action Virus
Direct action virus is a kind of virus where its primary purpose is to replicate or reproduce the file or folder. It takes proper action when the program is executed.
This virus waits for the particular file or program which is infected to start and then spreads the virus to other files in the directory or folder which are specified in the “AUTOEXEC.BAT” file path.
They often keep changing their locations into new files in the same directory and when every file is executed it shifts to another path to the directory.
In many cases, the batch file will be located in hard drives root directory, and it takes action when the computer booting process takes place.
The direct virus that is highly vulnerable:
Vienna: Vienna virus is a direct virus which is so destructive. It is the only type of virus among direct virus which is often called by its code name “DOS/Vienna.” It was evolved in late 1980, where it has been a severe
It was evolved in late 1980, where it has been a severe threat of virus at that time. This virus spreads by attaching its code to other files on your PC.
5. Directory virus
In the name itself, we can have a clear view that it affects the directories. The directory virus mainly infects the directory of your system by changing the file position or path to other locations.
Mostly, in this case of viruses, when the infected file or program is executed you will be running the virus program unknowingly. As the original file was altered or moved your file location to other location.
It’s almost impossible to find or locate the original files in your system, as the virus moved its position to other position and it always changes the position. So you can’t have a control on it.
This type of PC virus will be located in directory location itself, but the problem is if a directory hit by this virus it infects the entire program in that directory.
Directory virus which is highly vulnerable:
Dir-2 virus: Dir-2 virus is a directory virus which often tends to target directories. It is the oldest form of virus which is evolved in 1991 in Bulgaria.
Dir-2 virus loads the file which was attempting to execute and infects it. This virus has many other encrypted pointers to get access to the file’s actual location.
6. Boot Sector Virus
Boot sector virus is the most typical virus which affects the boot sector of a hard drive of your computer. It is the essential part of any system where the system information is stored, and it is also the important program which starts the computer or boots the computer.
Mostly these types of virus hide their appearance in the memory until the Disk operating system (DOS) got to access the floppy disc or disk. And once it accesses the floppy disk then whichever program is accessible this virus will infect them.
Boot sector viruses that are highly vulnerable:
AntiExe: AntiExE is a virus that infects the “master boot record” and “Disk operating system”(DOS). Antiexe original code name is “DOS/Antiexe” which is having a severe alert level. It was found in 1993, and its origin was Russia. It’s having a version of “AntiExE. A” to “Anti.ExE.c”
Polyboot: Polyboot is a virus which targets boot sector as well, and boot virus has also been renamed to “Polyboot.b” these days. It’s a malware which tends to access your floppy disk.
7. Companion Virus
Companion virus is also considered as the type of “File infector virus” and many call them as a resident or direct action types of virus. But it’s a separate virus which consists of both operations in a single virus.
This kind of virus is known as companion virus because “They accompany” the other files that already exist in your system. After that, they just carry out their infection process through affecting them and other programs as well.
Mostly these type of viruses are located in memory until it is executed. Once this virus executed it makes many copies of the virus itself, and it becomes pretty hard to find the original virus.
These types of viruses use the same names for their copies, but they change their file extension and create a new file extension for them. Suppose if you want to access a “program.exe”.
Then the virus names itself as “program.com” and shows up in your system. When you opt to execute this infected file “program.com” will be executed instead of “program.exe”.
Companion virus that is the high vulnerable virus:
Stator: W32/Stator@MM is also called as the stator which was evolved recently in 2013 and it is a virus which can even accompany your system restore files. The stator is the most recent model of Companion virus.
8. Multipartite Virus
The multipartite virus spreads in multiple ways and infects the programming files. They hide themselves into the memory like Memory resident virus and do affect the hard disk.
The multipartite virus which is highly vulnerable:
Flip: The flip virus is a multipartite virus which was evolved in the late 1990s from Germany, This virus has an interesting payload of flipping the screen horizontally.
Tequila: This is a multipartite virus which was notable in 1991, and it was destructive for its armoring techniques in the area of decryption. It’s a .exe file, and its origin was St.Hausen, Switzerland.
9. Polymorphic Virus
A polymorphic virus is a powerful virus that might guard itself with an encryption algorithm and has the tendency to change automatically when certain conditions are met.
Because of having the encrypting capability, it is tough to find it even with an antivirus program.
The polymorphic virus that is highly vulnerable:
Elkern: Elkern is a polymorphic virus in nature, and it was evolved in 2001 from China. It’s a different virus which produces in all types of .exe, .dll. .scr types. This virus often spread with the klezworm. Klez is another most destructive worms in history.
Marburg: Marburg is the polymorphic virus which often has many names, and its primary code name of the profile is “Win95/Marburg.8582”. It caused more troubles than other polymorphic types of virus.
10. FAT virus
FAT virus spoils the file allocation system section (Information where the location of data and the details of the available spaces are stored) and might cause significant damage to it. It would result in defeating the individual files or complete directories.
The fat virus that is highly vulnerable:
Link Virus: Link virus is a fat virus. It is a dangerous virus as it prevents actions to the main sectors of the hard disk. It has been named with various code names for ex: “virus:js.cer” worm: win32/sober.B@mm etc.
Not only these! There are still some common types of computer viruses like Web scripting viruses, time/logic bombs, Trojan horse virus, Rootkits, spyware, and worms have an affinity to disrupt the computer operation.
Most Dangerous Computer Viruses
In late 1980’s, computer viruses have started to born. Do you know about the first computer virus?
It is “The Brain” released from Pakistan in the year 1986. So the 25th anniversary of the first PC virus was marked in 2011.
The danger rating of the first computer virus is tiny, but the most dangerous viruses came into existence in 1990’s. Let’s check some worst types of computer viruses now.
Let’s check some worst types of computer virus programs now!
1. Code Red
A powerful worm named “Code Red” had made the anti-virus researchers in hindrance, and it infected millions of computers and lakhs of servers. It took advantage in Microsoft Internet information server too and was first detected by the employees of eEye digital security.
It is not necessary to open an email attachment or execute a file; it catches your PC if you open a particular web page.
2. Melissa
Melissa is a well-known worm that infected the MS Word document files through email attachments using MS outlook. This virus caused a severe destruction to the computers in 1999, and the damage was estimated at millions of dollars.
It had made the modern concerns like Intel and Microsoft temporarily to shut down.
3. My doom
My doom was considered a powerful virus in 2004 as it had the proficiency to stop accessing the antivirus program by the operating system. This virus spread through email with the text “Mail transaction failed” and gets downloaded into the system once the message got clicked.
Millions of computers were infected with this virus and loss was estimated in billions.
4. Nimda
Nimda virus had risen in the year 2001, and it is just the opposite form of the word “Admin”. This virus targeted to slow down the internet traffic, and it propagated to the system in different ways through emails, while sharing files, server weakness, etc.
Once this worm gets activated on the computer, the attacker would have the full control to the system if certain conditions are met.
5. Conficker
Conficker is the widespread internet virus and so the anti-virus researchers called it as “Super Worm”. This dangerous virus targeted Microsoft operating systems, and so millions of computer that had vulnerable Windows OS had hit by it.
This worst virus might spread through removable drives and assemble in such a way to take the financial and other vital data from the system.
If you’re are using the computer from long, then you might be aware of some other worst types of viruses like I love you (2000), Stuxnet (2009), agent.btz (2008), SQL Slammer (2003) and Blackworm (2006). Image credit: Flickr
Image credit: Flickr
Types of Computer Viruses in 2012
Now, check the different types of computer virus programs that caused significant damage to the computers in the year 2012.
Shamoon
Shamoon was discovered in August 2012 that has been used for cyber spying. It infects the system runs on Windows NT, Windows me and Windows 9x. The attacker uses the “dropper” function to spread in the network to the hard disk of the computer so that to compile the list of files on attacked computers.
Then the attacker receives the data with the help of “reporter” program. “Wiper” is the function used to erase the involved files and this might create problems in booting by overwriting action.
Gauss
Gauss is the highly destructive computer worm which was intentionally created to steal the data from Middle-east banks. It was discovered in June 2012 by a Russian lab, and it affected thousands of computers.
It can infect the USB drives, and collected information will be stored as a hidden file on the removable drives.
DNS Changer
Cyber-criminals created this virus to redirect the internet traffic to a phishing website. The DNS changer computer virus modified the Domain Name System (DNS) configuration of computers and redirects the users to a specific website.
FBI got involved in this virus, and the interim servers were officially shut down on July 9, 2012.
Belgian
Belgian is the worst computer virus spreads through spam emails or hacked web pages. It locked the computers and then asked for some money to unlock the data.
This global virus has the power to gain the remote access to computers to track the files and launch the malware when Windows gets started.
Flame
Flame is the sophisticated malware found in 2012 which used Bluetooth to send commands. It was discovered in Russian lab, and it grabs the data from chats, emails, and screenshots.
It steals sensitive data and infects many computers in Iran and Middle East countries.
Many types of computer viruses are being created every day, and the new computer virus like Ransomware (freezes the PC and ask to pay ransom to unlock) have started to cause damage to the computer this year.
Even though the anti-virus researchers are working to prevent these actions with powerful anti-virus software, cyber-criminals are tactically creating the malware.
Read the Economic Times article related to Ransomware
Most Recent & Dangerous virus 2016
Ransomware
Ransomware is the malware which caused damage worth millions of dollars for larger firms to smaller firms.
It is evolved in Russia, and it became broadly popular in Russia, by infecting thousands of systems and spreading the infection like a viral infection.
Ransomware is a type of malware which gets installed on your computer unknowingly or without any knowledge. It stops your system working from your access and makes the system display error message. The system will only return to the normal stage when you pay some amount to that firm.
There are two types of ransomware!
1. Encrypting Ransomware
Encrypting Ransomware is the virus which encrypts all the data of your system and demands a ransom to UN-encrypt the files.
Encryption ransomware is created on the base of crypto virology and more. So to decrypt the algorithm it would take some years to bring the system to the normal level. Many people have fear towards this virus and pay millions of dollars.
2. Non-encrypting Ransomware
Non-encrypting ransomware is the virus which does not encrypt your files and data. But it blocks your access to your computer and shows you the irritating messages. This is not that powerful as compared to other ransomware. It can be protected by taking a backup of general files and installing the system software again.
Trojan-Skelkey
Trojan-skelkey was the recently arisen virus in 2015, and it has more attacks in 2016. Trojan.skelky is a Trojan type virus where the Trojan horse allows the attackers to secretly log in as any user on the infected and compromised system or computer even with a wrong password.
This virus was discovered on January 13, 2015. Since then it is affecting a lot of systems and increasing its name by attacking more and more systems.
Exploit-SWF.x
Exploit-SWF.x is a generic detection for a Trojan, and that is the part of the Angler exploit kit. This new computer virus was evolved on 2015 and is being mostly used in 2016 by attackers to take down systems.
This type of computer virus is also called as Hoax.
Conclusion
How Vulnerable Are We?
With new technology advancements, highly skilled programmers invent several types of computer viruses to damage our computer or to steal information from it. Computer Viruses are the well-known computer attackers, and they can drastically slow down its operation.
Moreover, due to the natural installing nature of malicious programs, computer users suffer from the data loss and system disruption. So it is essential to take some security measures by installing efficient anti-virus software to ensure your computer protection.
I had been greatly suffered by some types of computer viruses last year. Now I protected my system with the best virus removal software, Quick Heal Total Security Antivirus tool.
It has some advanced programs and upright in system cleaning. I suggest you opt premium virus protection than using free anti-virus software.
Kaspersky, Bitdefender, and Norton are some of the well-known brands of premium PC security software and good to know that AntivirusInsider has some great deals on Bitdefender that would help to save your hard-earned bucks.
I hope that you’ve gained some knowledge about the types of computer viruses and their painful effects through this post.
So, have you recognized several computer virus names? What is your opinion about this computer virus list? Share your insights about this list of computer viruses in the comment section.
If you have any bitter experience with the PC intrusion codes and Malware, share that as well!

Hi Nirmala.
Good breakdown here buddy. I had a virus a few weeks ago here in Pondicherry. It was rough! I was really sick to my stomach but after a few days all was good.
Similar effects plague your computer if you catch a virus. As you said, get the proper protection, educate yourself and please, no clicking on untrusted links.
Unless you know a person well never click on attachments. Even if you do know a person well and the attachment seems suspicious, call them or connect with them through some other social network to verify if they in fact sent it.
Great tips buddy, thank you.
Ryan
I felt hard with your sickness, take care Ryan.
Thanks for leaving your advice for the computer users and it added some value to my post.
I really happy to see that you’re my opening commenter for my every blog post.
Keep doing it, so that i’ll stay motivated 😉
Madam this article is so depth that makes us to get each and every virus clearly. Thanks for pointing out. I have good experience with these. And never for browsing in internet without installing anti virus. These would surely give a bad impact in our system.
Notepad also helps to detect some viruses. Pointing out latest computer viruses in 2012 also wonderful. An updated article on computer Trojans thanks.
Thanks for appreciating my post Tharun, yeah, I had intentionally written that for the computer user to prevent the dangerous viruses.
Glad you find this post useful and thanks for sharing your views.
Hey,
I haven’t suffered from any dangerous computer virus yet. But it’s the worst feeling when any virus gets activated in your computer. It’s better to do all possible security measures before any virus reaches you. I really got some good knowledge about computer viruses from this write-up 🙂 Wonderful Article, Thanks 🙂
Glad you’ve gained some knowledge about computer viruses through my post Siraj 🙂
It is really good that you haven’t met any viruses in your computer.
Thanks for your comment and keep coming here to share your real experiences 🙂
What hurts me most is viruses from emails. I have never understood why the email address providers can’t find a way to deal with this things and people who post and send them. I once experience two tough days because of opening an email in 2011, ‘A total damage’ I had not backed up my infor and you can bet the pain I went through plus spending money which I had not planned. I learnt my lesson. Thanks for sharing ~ Anetta
Hi Anetta,
Welcome to my blog and thanks for sharing your bitter experience about the email viruses with me.
Yeah, hackers are really smart these days and they are finding the powerful sources to attack the PC. So they might chose “Emails” to spread viruses.
Keep visiting here to leave your thoughts Anetta 🙂
I have a advice for you guys that if your computer data is very much important,then you should have to use premium antivirus for your system.
Because free antivirus clean up your computer up to a certain limit….
thanks for sharing it….:)
Thanks for your comment and advice Vishu, keep showing your presence here to leave your suggestions 🙂
From my experience, sometimes you might not even know that your computer is infected with a virus. I also met a lot of people who believe that having an antivirus software on the computer can protect them from anything on the web so they go clicking any link they find, harmful or not.
I wish more people realized that antivirus reduces the chances of getting a virus, but doesn’t completely eliminate it. New viruses are being written every day, and antivirus software is just playing catch-up most of the time.
Yeah, well-said Aliaksandra.
I agree with this and so advising the PC users to use premium anti-virus software atleast to decrease the chance of getting virus.
I appreciation your worthy comment, keep coming to do the same 😛
Very good point, there is a reason why some companies provide two versions of their antivirus: a free and a paid version. Free version is a bare minimum, many times only intended to recognize the virus, but cannot protect from it or remove it from the PC. Premium versions ensure the best level of protection.
I really like your lightning fast reply and appreciate it too.
Hope you’re adding more value to my post. Are you there on FB or G+ to connect?
For removing computer viruses i always recommended every people to use MSE (Microsoft Security Essential) It is really good in removing the hazardous viruses.
Thanks for your recommendation Kartik, stay tuned here 😛
Hi, Nirmala Mam,
Indeed very informative post. 🙂
Yes, viruses are very dangerous for personal computers and personal data. Through these malicious programs, hackers try to reach our data and then they hack.
These programs mainly come from untrusted source or mail on internet.
Know about these Viruses can helps us in saving our vital information from being hacked.
Thank you very much for sharing such a wonderful Post.
Have a great weekend. 🙂
Thanks for your encouraging comment and glad to read your views related to computer viruses 🙂
Leave your useful reply as always Kumar Chandan 😉
Hi Nirmala !
I feel that there are many computer users who don’t have any idea about the extent of damage a virus can do to their computers and this is the best post for them.You’ve done right thing by sharing these all points through your blog . Thanks for sharing .
-Pramod
Yeah, computer viruses are very dangerous. They could corrupt the OS and files and pushes the PC users to experience a great data loss and inactivity.
So, presented this post just for the awareness of malicious programs.
Thanks for commenting here Pramod, am happy with your regular visit 🙂
Dealing with virus is one of the difficult tasks anyone could deal with and it is something many of us have to deal with so far as we continue using computers!
Am confused with your comment. What you’re trying to conclude Emmanuel?
Anyway, thanks for reading my post and leaving your comment 🙂
Hello Nirmala Ji
Thanks for giving deep information about virus and their conclusion.
Good to hear that you felt the deepness of this post, keep coming here Chetan
Hello,
Awesome post, really informative. I don’t know about the virus stuff completely now i gained the complete information about.
Thanks for sharing.
Glad you’ve gained some information related to computer viruses through this post, keep coming here Anirudh Karthik 🙂
“great efforts”
Thank you for sharing such a brief description about computer viruses.
Very nice list of viruses. Really we have to prevent all these problems. Nirmala, you got a very nice blog. I think India will definitely top the list in quality blogging field. Thanks for this information.
That’s why a good antivirus is must. Macros are very dangerious for office employees and some similar usb virus that infect system32 file on windows.
excellent article but detailed version can be found here
http://www.cryptprogramming.com/2015/09/different-types-of-computer-viruses-and-their-effects/
This web hlep me in my school project. The lanuage is very easy.
It is best lines of different types of computer virus and there harmfu’ll effect
Hai mam thanks for your information. I am studying 7 std. I have read this for my cs project. I hope I will get full marks in my project.once again I thank you
Great stuff! You have written an awesome article. It contains lots of information which is very helpful for me. Thanks
Nirmala madam,
Thanks for blogging about antivirus types. Very well explained. Can you suggest me some good antivirus softwares. I am using Windows 10 Home edition.
You may buy, Quick Heal Total Security! I’m using it for both Mac and Windows. It is a great Antivirus software to protect the PC and other computing gadgets!